The utilization of the term Virtual Treason in the context of reporting on the Iran-U.S. conflict signals a shift from conventional political critique to a deliberate strategy of institutional erosion. When an executive actor labels media coverage of military tension as treasonous, they are not merely debating facts; they are reclassifying dissent as an existential security threat. This maneuver operates through a specific structural framework designed to consolidate narrative control by increasing the political and social cost of adversarial reporting.
The Architecture of Information Control in Conflict Zones
In modern geopolitical friction, the battlefield is bifurcated between kinetic military action and the information environment. The "Virtual Treason" framework relies on three distinct pillars to alter the public’s perception of conflict:
- The Sovereignty Monopoly: This principle posits that the executive branch is the sole legitimate arbiter of national security reality. Any media organization offering a counter-narrative—such as questioning the legality of a strike or the imminence of a threat—is framed as providing "aid and comfort" to the adversary.
- Digital Decoupling: By labeling coverage "virtual," the actor suggests that the information exists in a space where traditional protections (like the First Amendment or journalistic privilege) are subordinate to the immediate needs of the digital information war.
- The Penalty of Ambiguity: By using high-stakes legal language like "treason" in a non-judicial context, the speaker creates a chilling effect. The objective is to force news outlets into a defensive posture where they must prove their loyalty rather than their accuracy.
Quantifying the Information Feedback Loop
The relationship between media coverage and military escalation functions as a feedback loop. In the specific case of U.S.-Iran relations, the "Virtual Treason" accusation targets the Verification Lag—the time it takes for independent journalists to confirm or debunk government claims.
The cost function of this strategy is measurable through audience polarization. When the media is labeled a traitorous entity, the consumption of news shifts from an act of information-seeking to an act of tribal affiliation. This creates a bottleneck in the democratic process: if the electorate cannot agree on the basic sequence of events regarding a drone strike or a naval skirmish, the government can operate with significantly reduced oversight.
Structural Failures in Wartime Journalism
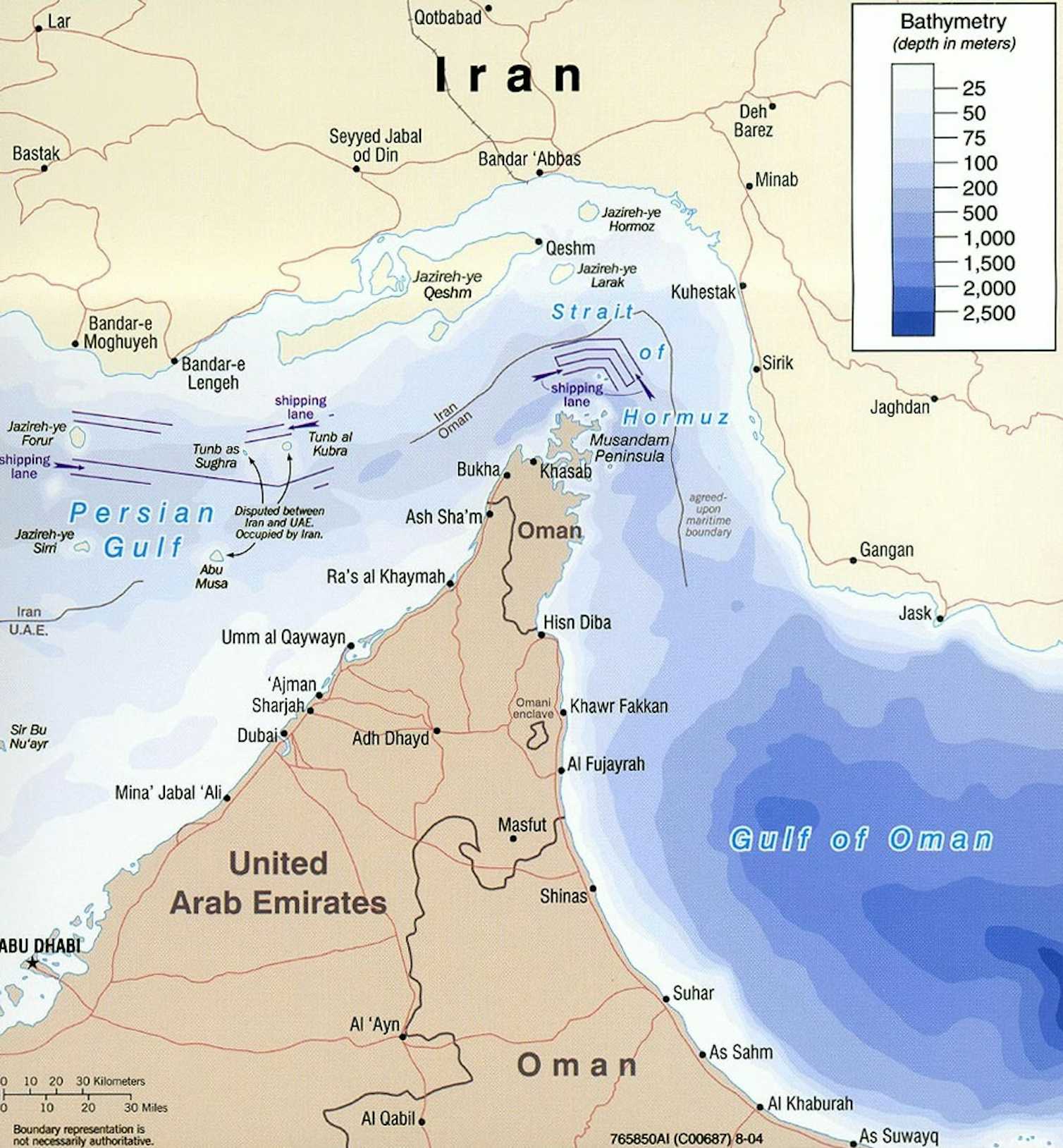
The competitor’s assertion that the media is biased fails to account for the Asymmetry of Access. In conflict zones like the Persian Gulf or the Strait of Hormuz, the government controls the physical platforms (ships, aircraft, satellites) required to gather data. This creates a structural dependency.
- Intelligence Leakage: Media outlets often rely on "senior officials" for scoops. When the administration turns on these same outlets, it signals a strategic pivot from "controlled leaks" to "blanket denial."
- Narrative Displacement: By focusing the public’s attention on the "treasonous" nature of the media, the administration successfully displaces the primary debate regarding the efficacy or legality of the military strategy itself.
- The Echo Chamber Multiplier: Social media algorithms prioritize high-arousal content. Accusations of treason generate 10x more engagement than technical corrections about missile range or troop movements, ensuring that the delegitimization reaches a broader audience than the original news report.
The Semantic Reclassification of Treason
Historically, treason is a narrowly defined legal concept requiring an overt act and two witnesses. In the "Virtual Treason" era, the definition is expanded to include:
- Cognitive Dissonance Induction: Reporting on Iranian casualties or civilian impact is framed as humanizing the enemy.
- Strategic Skepticism: Questioning the "intelligence" behind a strike is rebranded as sabotaging the mission.
- Operational Exposure: Even if the information is already public, the act of synthesizing it into a critical analysis is viewed as providing a tactical roadmap to the adversary.
This expansion serves a specific function: it lowers the threshold for executive retaliation. While a formal treason charge would fail in court, the social and commercial "conviction" in the court of public opinion is instantaneous and requires no evidence.
The Economic Impact of Narrative Hostility
For media organizations, the cost of being labeled a national enemy is not merely reputational; it is financial.
- Cyber-Security Expenditures: Outlets targeted by high-level political rhetoric see an immediate spike in state-sponsored and vigilante cyber-attacks, necessitating increased spend on digital defense.
- Insurance and Liability: Reporting from conflict zones becomes exponentially more expensive when the home government refuses to provide standard protections or logistical assistance to "hostile" press.
- Market Fragmentation: Advertisers increasingly avoid "politicized" news cycles, leading to a revenue drain for hard-news investigative units.
Tactical Response Systems for Information Integrity
To counter the "Virtual Treason" strategy, media organizations must transition from a reactive "fact-checking" model to a Proactive Verification Architecture. This involves:
- Open-Source Intelligence (OSINT) Integration: Relying on commercial satellite imagery and shipping data to bypass government-controlled information channels.
- Transparent Sourcing Protocols: Clearly categorizing every piece of information as "Direct Observation," "Verified Third Party," or "Government Assertion."
- Decentralized Distribution: Utilizing blockchain or peer-to-peer networks to ensure that "virtual" reporting cannot be de-platformed by executive pressure on tech monopolies.
The "Virtual Treason" rhetoric is a symptom of a larger geopolitical trend where the control of the narrative is prioritized over the control of the territory. In a world of perpetual grey-zone conflict, the media is no longer an observer; it is a combatant in the eyes of the state.
The most effective strategic counter is not to argue the "loyalty" of the press, but to demonstrate the Utility of Dissent. A state that operates without an adversarial press lacks the feedback mechanisms necessary to avoid catastrophic strategic errors. The media’s role in a conflict is to serve as the external audit of the state's kinetic power. When that audit is labeled treason, the state is essentially announcing its intention to operate without a safety valve, increasing the probability of unintended escalation and systemic failure.
To mitigate the risks of this environment, organizations must treat information security as a primary operational pillar, diversifying their data streams and insulating their reporting from the volatility of executive rhetoric. The goal is to move the conversation from "loyalty" back to "accuracy," forcing the state to compete on the field of verifiable facts rather than emotional provocations.